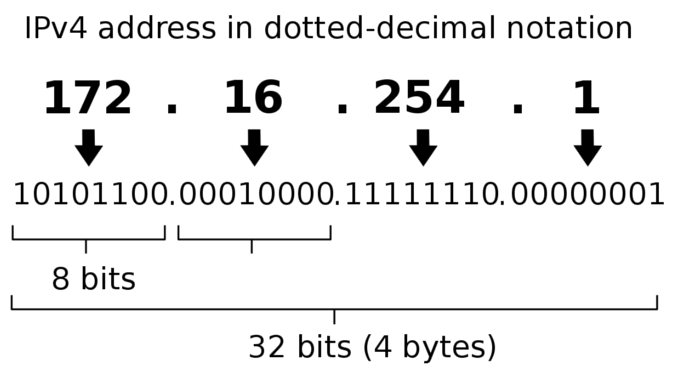
Internet Protocol version 4, commonly referred to as IPv4, is the fourth version of Internet Protocol (IP) addresses. It was developed in 1981 by DARPA – The Defense Advanced Research Projects Agency, which is an R&D agency of the U.S. Department of Defense.
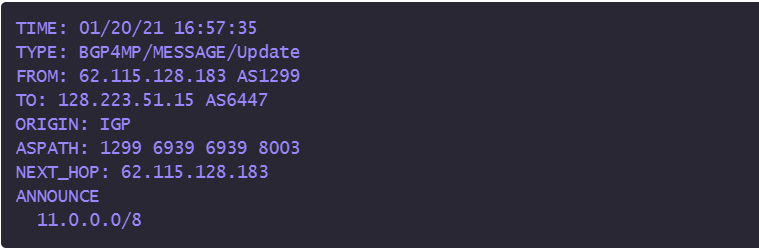
Moments after Joseph Biden was sworn in as 46th President of the United States and three minutes before the official statutory end of Donald Trump’s term on January 20, 2021 the University of Oregon’s Route Views Project recorded data from a company registered on September 14, 2020 as GRS – DOD as it announced itself with an explosion of previously unused IPv4 addresses owned by the Department of Defense in the tens of millions.
According to Doug Madory, director of Internet analysis for Kintik Blog, who was among those trying to figure out what was happening, said “they are now announcing more address space than anything ever in the history of the Internet.”
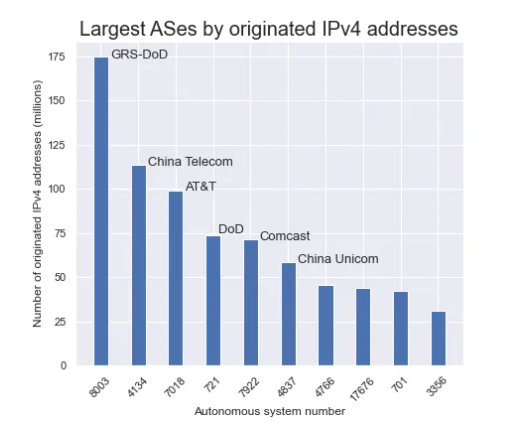
About 56 million address space in late January has now grown to about 175 million.
The questions that started to surface included: Who is AS8003? Why are they announcing huge amounts of IPv4 space belonging to the U.S. Department of Defense? And perhaps most interestingly, why did it come alive within the final three minutes of the Trump administration?
By late January, AS8003 was announcing about 56 million IPv4 addresses, making it the sixth largest AS in the IPv4 global routing table by originated address space. By mid-April, AS8003 dramatically increased the amount of formerly unused DoD address space that it announced to 175 million unique addresses.
Following the increase, AS8003 became, far and away, the largest AS in the history of the internet as measured by originated IPv4 space. By comparison, AS8003 now announces 61 million more IP addresses than the now-second biggest AS in the world, China Telecom, and over 100 million more addresses than Comcast, the largest residential internet provider in the U.S.
Kentik Blog: The Mystery of AS8003
Madory wondered if Congress had finally forced DoD to sell this precious Internet real estate commodity. In 2019, Congress attempted to slip a provision into the 2020 NDAA requiring the Pentagon to sell off all of this valuable asset over 10 years at fair market price before it could pass. The CBO estimated an eighth, ~16.7 million addresses, was valued at about $100 million ‘after transaction fees.” That provision was stripped out before passage ‘and the DoD would be funded without having to sell one of its most precious assets.’
Another question arising, who was the mystery portion GRS in the GRS-DOD who keeps adding billion of dollars worth of this real estate to the Internet and is now at the top of the AS (autonomous system) chart, something that is usually the domain belonging to the top telecommunication companies?
The company that was first registered on September 14, 2020, according the Washington Post, is Global Resource Systems LLC, a company “that has no publicly reported federal contracts and no obvious public-facing website” appears to be a shell company.
As listed in records, the company’s address in Plantation, Fla., outside Fort Lauderdale, is a shared workspace in an office building that doesn’t show Global Resource Systems on its lobby directory. A receptionist at the shared workspace said Friday that she could provide no information about the company and asked a reporter to leave. The company did not respond to requests for comment.
Washington Post
Speculation and concern about possible hacking or fraudulent hijacking “of almost all DoD prefixes” being announced under the newly formed “GRSCORP” or the Border Gateway Protocol (BGP) – “the messaging system that tells Internet companies how to route traffic across the world” were picked up by NANOG listserv contributors. The data recorded by University of Oregon’s Route View Project was a message “telling network administrators that IP addresses assigned to the Pentagon but long dormant could now accept traffic — but it should be routed to Global Resource Systems.”
That has now been ruled out as the DoD has provided “an answer, of sorts” to the Washington Post on Friday.
The change is the handiwork of an elite Pentagon unit known as the Defense Digital Service, which reports directly to the secretary of defense. The DDS bills itself as a “SWAT team of nerds” tasked with solving emergency problems for the department and conducting experimental work to make big technological leaps for the military.
Created in 2015, the DDS operates a Silicon Valley-like office within the Pentagon.
…
Brett Goldstein, the DDS’s director, said in a statement that his unit had authorized a “pilot effort” publicizing the IP space owned by the Pentagon.“This pilot will assess, evaluate and prevent unauthorized use of DoD IP address space,” Goldstein said. “Additionally, this pilot may identify potential vulnerabilities.”
Goldstein described the project as one of the Defense Department’s “many efforts focused on continually improving our cyber posture and defense in response to advanced persistent threats. We are partnering throughout DoD to ensure potential vulnerabilities are mitigated.”
Washington Post
Madory describes it like this:
I interpret this to mean that the objectives of this effort are twofold. First, to announce this address space to scare off any would-be squatters, and secondly, to collect a massive amount of background internet traffic for threat intelligence.
On the first point, there is a vast world of fraudulent BGP routing out there. As I’ve documented over the years, various types of bad actors use unrouted address space to bypass blocklists in order to send spam and other types of malicious traffic.
On the second, there is a lot of background noise that can be scooped up when announcing large ranges of IPv4 address space. A recent example is Cloudflare’s announcement of 1.1.1.0/24 and 1.0.0.0/24 in 2018.
For decades, internet routing operated with a widespread assumption that ASes didn’t route these prefixes on the internet (perhaps because they were canonical examples from networking textbooks). According to their blog post soon after the launch, Cloudflare received “~10Gbps of unsolicited background traffic” on their interfaces.
And that was just for 512 IPv4 addresses! Of course, those addresses were very special, but it stands to reason that 175 million IPv4 addresses will attract orders of magnitude more traffic. More misconfigured devices and networks that mistakenly assumed that all of this DoD address space would never see the light of day.
Conclusion
While today’s statement from the DoD answers some questions, much remains a mystery. Why did the DoD not just announce this address space themselves instead of directing an outside entity to use the AS of a long dormant email marketing firm? Why did it come to life in the final moments of the previous administration?We likely won’t get all of the answers anytime soon, but we can certainly hope that the DoD uses the threat intel gleaned from the large amounts of background traffic for the benefit of everyone. Maybe they could come to a NANOG conference and present about the troves of erroneous traffic being sent their way.
